
COOKIE COOKIE GIVE ME A COOKIE
When you click "Accept All Cookies" on a cookie consent banner, a single click authorizes over 1,200 ad tracking companies and data brokers to collect your browsing history, GPS location, and personal data. This cybersecurity explainer shows how cookie tracking, the Meta pixel, in-app browser surveillance, and infostealer malware actually work, and gives you five browser privacy steps you can do in under a minute each.
It starts with my dad. Mikhael Kollander played guitar for The Andy Williams Show in 1969. A guy in a bear costume walked onstage every week begging for cookies. That same year, a programmer at MIT named the world's first piece of malware after it. 57 years later, that word is why your data sells for $10 on underground marketplaces.
Instagram and TikTok inject tracking code into every link you tap inside their apps. Your ad blocker doesn't work inside their built-in browser. A $200/month infostealer subscription called Lumma infected 394,000 computers in two months. One stolen session cookie led to the theft of 780 gigabytes of EA's data, including the FIFA 21 source code. The FBI called the takedown "Operation Cookie Monster."
Five steps to protect your online privacy. Apple App Tracking Transparency. Opening links in Safari instead of in-app browsers. Switching from Chrome to Firefox or Safari. Passkeys. uBlock Origin. Less than a minute each.

She Knew Exactly What Was Wrong. She Couldn't Say a Word
What happens when every institution you look at is set up to reward the wrong thing. On healthcare, cybersecurity, insurance, and incentive structures.

She Thought She'd Lose Her Job. Instead, They Promoted Her
A family-run company acquired my sister's employer and planned to let her go. Then they met her. What happened next rewired how I think about business ownership.

Let's Talk About the Women Behind the Build 🏆
For Women's History Month 2025: instead of talking about what I'm building, I wanted to spotlight the brilliant women who are actually building it. Yaara, Adi, Liat, Shwetha, and Laura at Axis Security, Silver Peak, and HPE Aruba. The best product decisions come from teams that reflect more perspectives, not fewer.

Great Security Starts with Great Design 🧸✨🔐
Cybersecurity is full of serious tools that are seriously hard to use. When something breaks, it's usually not the tech: it's the config. And that's how security fails. This is the story of why Axis Security built differently: one policy UI, design-led culture, and toys on every desk. And why HPE bought us for $500 million. 🦕

🧠 Pattern Recognition > Mismatched Socks
I'm Autistic and ADHD, which means my brain doesn't look tidy. But pattern recognition rarely is. We've always been the ones who noticed what others missed and saw the break coming before anyone else could blink. Today we're engineers, architects, founders, and VPs, not despite how our brains work, but because of it. That's how you define leadership, no matter what socks you're wearing
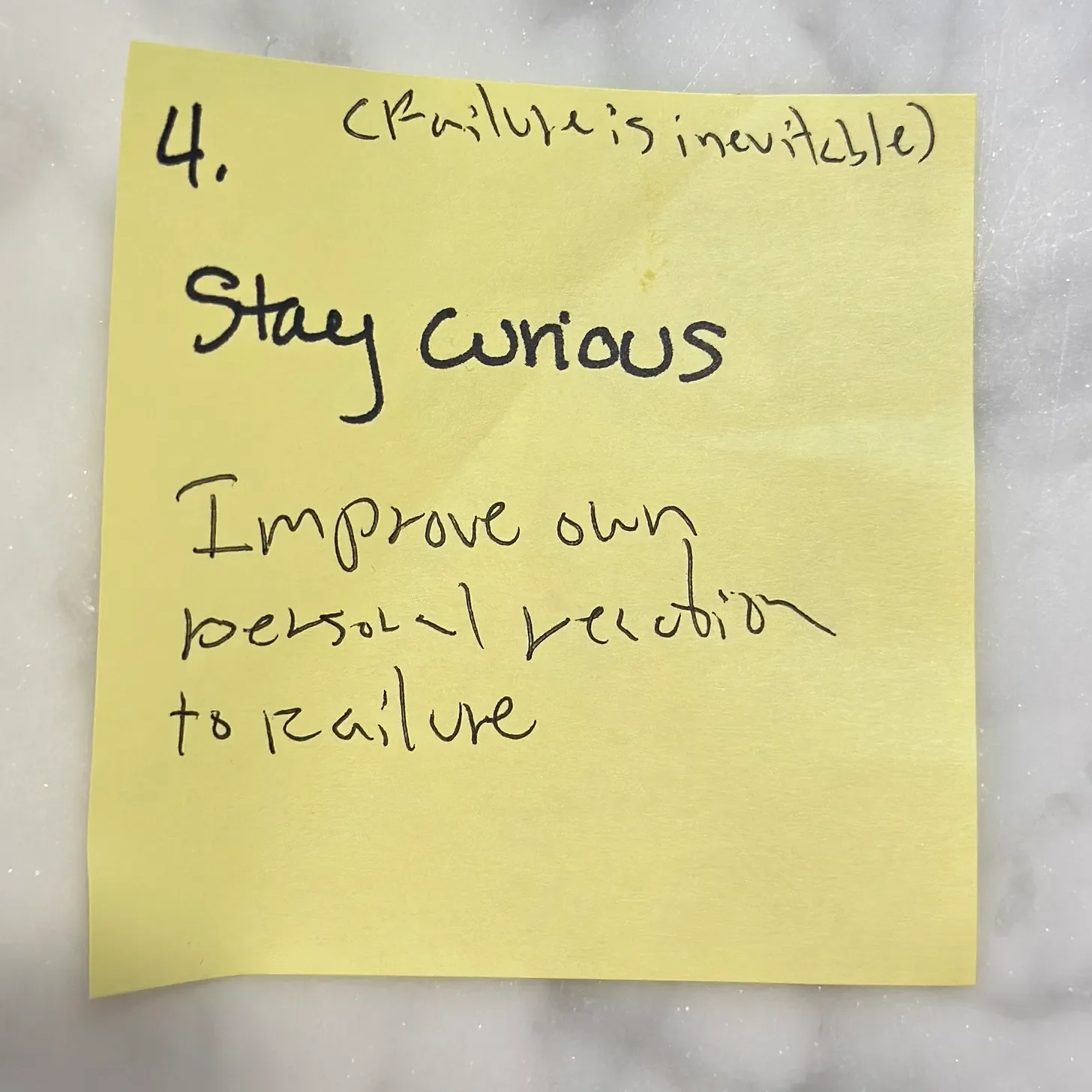
Failure Isn’t the Detour: It’s the Road
After twenty years in tech, I've learned that failure isn't the thing standing between you and the goal: it's baked into the road itself. This piece is about designing your response to failure instead of pretending you can avoid it: staying curious over controlling, measuring outcomes over output, and building with people willing to fail out loud. It came out of a Collaborative Gain exercise that stuck with me, and it applies way beyond product teams.
Herbs, Eggs, a Siren
First breakfast in Tel Aviv.
Here for a 🏳️🌈 wedding, family, and maybe a few new beginnings.
Herbs, eggs, coffee.
No music. No narration. Just (mostly) quiet sound.
I cooked simple food and cleaned as I went, a ritual I picked up from my dad on job sites. 👷🏻🛠️
I think a lot about him when I’m here. The people, the food, the music…it all reminds me of the best parts of him.
At 11 am, the air sirens sounded for Yom HaZikaron (Memorial Day).
Everything paused.
This was the quiet before that moment. 💙